Overview
Kpow supports Jetty (File, LDAP, DB), SAML, OpenID and OAuth for authentication.
Read on to learn how to easily integrate Kpow with Okta, AWS SSO, Microsoft Entra ID, GitHub, Keycloak, and more.
Jetty authentication
Kpow is built on the Eclipse Jetty Web server.
See: Application Logs guide to enable Jetty JAAS Debug Logging.
Set HTTP_FORWARDED=true when running Kpow behind a proxy with Jetty authentication
Jetty provides a number of JAAS (Java Authentication and Authorization) integrations including:
- PropertyFileLoginModule: user credentials are stored in a property file.
- LdapLoginModule: user credentials are stored in LDAP.
- JDBCLoginModule: user credentials are stored in a DB accessed via JDBC.
- DataSourceLoginModule: similar to JDBC but uses a JNDI Datasource to connect to the DB.
Kpow supports all of these Jetty JAAS integrations. Details of each are in this guide.
SAML authentication
Kpow is easily configured to be a Service Provider and integrates with any SAML Identity Provider, we include specific integration guides for Microsoft Entra ID, Okta, AWS SSO, and Keycloak.
Note: When running Kpow with a reverse-proxy for HTTPS termination (rather than HTTPS Connections) care must be taken with the scheme of configured authentication URI.
OpenID and OAuth 2.0 authentication
Kpow supports integration with Okta (OpenID) and GitHub (OAuth 2.0) SSO providers as well as generic providers. See: OpenID Connect.
Need a Provider Added? Just email support@factorhouse.io and we'll estimate delivery.
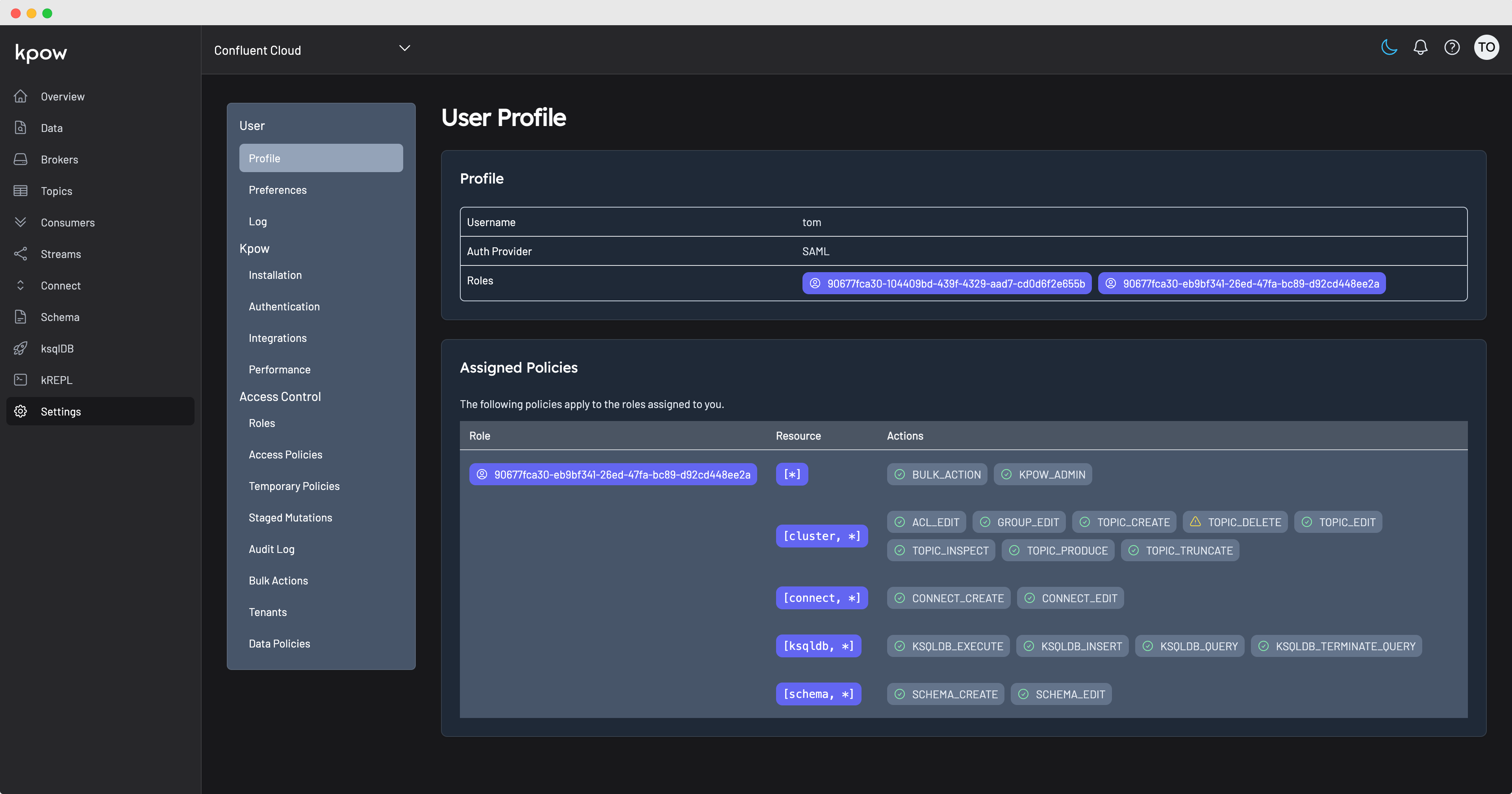
Kpow and User authentication
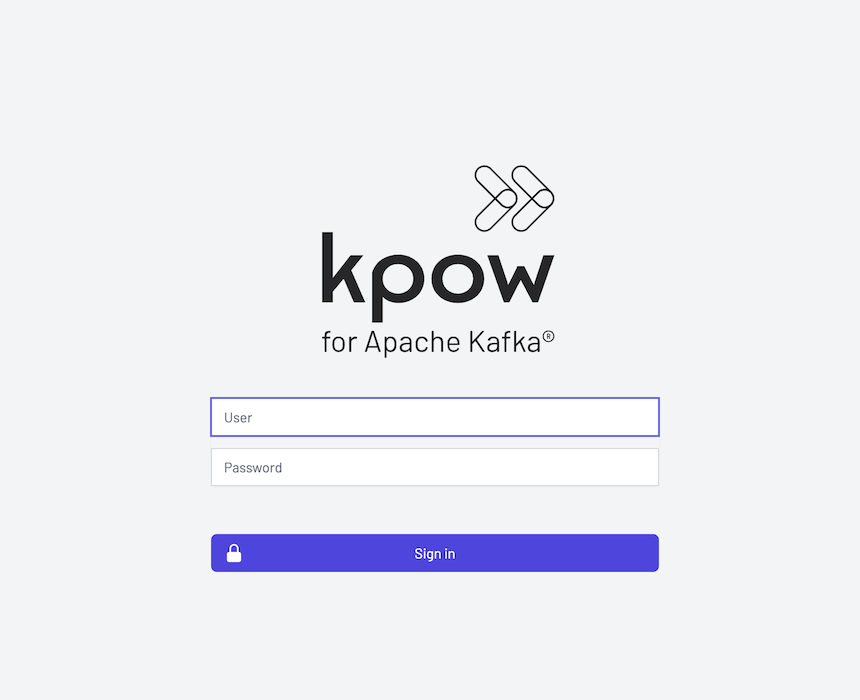
With authentication configured Kpow requires all users to authenticate prior to accessing the UI.
Note: Access to Prometheus endpoints remains unauthenticated.
When Jetty authentication is configured users will be prompted with form-based or basic login prompts.
Regardless of the mechanism used for authentication, all users can view their profile information.